I have encountered the following error message when I was trying to connect Jenkins slave after plugin update:
[SSH] WARNING: No entry currently exists in the Known Hosts file for this host. Connections will be denied until this new host and its associated key is added to the Known Hosts file.
Key exchange was not finished, connection is closed.
java.io.IOException: There was a problem while connecting to xxx.xxx.xxx.xxx:22
I have tried to connect using ssh in console, it connected successfully, but Jenkins still refuse to connect.
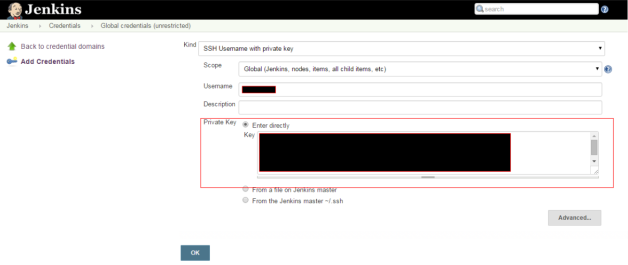
Then I discovered that, if I provided the RSA Host key, Jenkins can now connected to slaves.
I guess the reason is ssh just use the known host key to determine whether it is known, and be able to fallback to RSA for actual authentication. On the other hand, Jenkins does not seem to have the fallback. You given RSA identity, then Jenkins expect RSA in known_hosts.
The issue is already filed as JENKINS-42959 Failed known_hosts verification for SSH agent. In the meantime you can use following workaround:
stdbuf -o0 -e0 ssh-keyscan -H <host> &>> ~/.ssh/known_hosts
The stdbuf here is for printing the stdout and stderr as the order of time they appear, just like what you would see in console. Otherwise the stderr will go first and then stdout.